1712 LESSON Sun Dec 13 2015
FREE Online A1 (Awakened One) Tipiṭaka Research & Practice University (FOA1TRPU) & Social Transformation Volcano (STV) NEWS through
http://sarvajan.ambedkar.org
in
92 CLASSICAL LANGUAGES

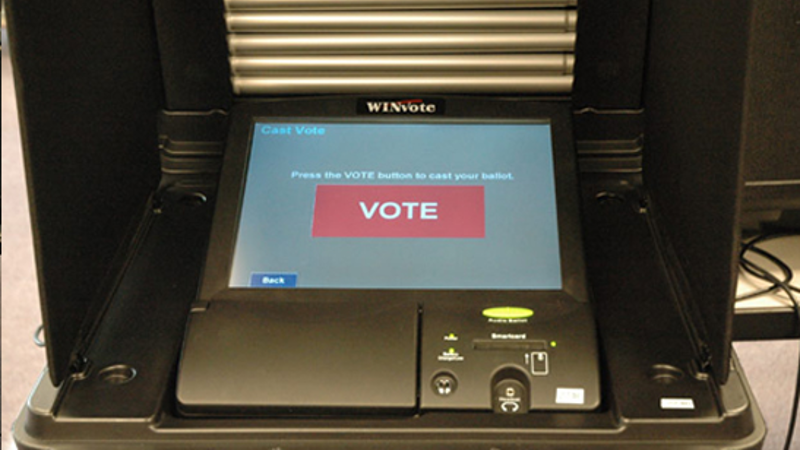

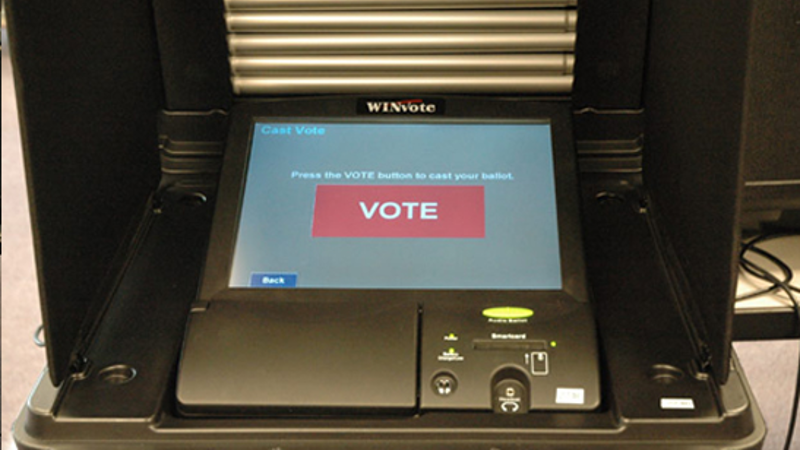
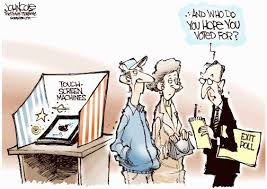
Electronic voting machines used for US elections between 2002 and
2014 would have been extremely easy to hack, according to reports.
The AVS WinVote machines were used during three presidential
campaigns in the state of Virginia and would receive an “F-minus” for
security, with many using “abcde” or “admin” as passwords.
Jeremy Epstein, of non-profit organization SRI International, who
served on the Virginia state legislative commission and has been
investigating the machines for some time, is relieved that they have now
been decertified.
“The vulnerabilities were so severe, and so trivial to exploit, that
anyone with even a modicum of training could have succeeded”, he explained.
“They didn’t need to be in the polling place — within a few hundred
feet (e.g., in the parking lot) is easy, and within a half mile with a
rudimentary antenna built using a Pringles can. Further, there are no
logs or other records that would indicate if such a thing ever happened,
so if an election was hacked any time in the past, we will never know”.
In an interview with the Guardian,
Epstein also explained that his conversations with Brit Williams, the
original certifier of the voting machines, had been equally concerning.
“I said, ‘How did you do a penetration test?’ and he said, ‘I don’t know how to do something like that’”.
The Virginia Technology Agency today published a report condemning
the WinVote machines, which have also been used for elections in
Mississippi and Pennsylvania. It found that the machines ran a version
of the Windows operating system that had not been updated since 2004,
leaving them susceptible to relatively simple malware and hacking
attempts.
The news comes at a time when the UK is preparing for its own vote,
with the general election scheduled for next month. Although electronic
voting, or e-voting will not be available this year, it is reported to
be in place for the 2020 election.
Published under license from ITProPortal.com, a Net Communities Ltd Publication. All rights reserved.
-
Driven
•
8 months ago
anyone this is a surprise to hasn’t been paying attention. http://blackboxvoting.org/ has said this since 2004 and it is not exclusive to this one type of voting machine. It is trivial to exploit any of them.
Daniel
•
8 months ago
Want to know a funny thing? The Brazilian voting machines already
come rigged, so the winner’s are already decided from the get go.
-
Eric Sleeper
•
8 months ago
Once I figured out that non-US citizens and people illegally here
(even worse) can vote, I have lost all hope on the election process.
Even a worse opinion of the politicians that continue to argue that no
real form of ID is required. Once you figure this out, you start to see
it’s hacked before even getting to the voting machines.
sgrandin
•
8 months ago
Been known and reported on for many years. In fact, there have been
claims that hacking has already occurred in some elections. But this is
capitalistism, where voting is mostly for show, to keep the masses
thinking they determine things.
-
korfuntu
•
8 months ago
It is WAY past time for Congress to establish a non-partisan
standards committee for electronic voting machines, composed of experts
from all relevant technology components. This committee would create
mandatory security standards that ALL electronic voting machine
manufacturers must meet before their products can be used in any
election where Federal office holders are elected.
And while they are at it, they might start working on hack-proof standards to allow Internet voting.
This is the 21st century. It’s time we started acting like it.
Bob Grant
korfuntu
•
8 months ago
First off, there is no such thing as ‘hack proof’. Anything can be hacked.
Second,
I wouldn’t trust the government to pick out the right nail to hang a
wall calendar, much less “experts” on technology. (I would trust their
chosen standards far less)
Proof No 17

http://www.popsci.com/gadgets/article/2012-11/how-i-hacked-electronic-voting-machine
How I Hacked An Electronic Voting Machine
What do you need to rig an election? A basic knowledge of
electronics and $30 worth of RadioShack gear, professional hacker Roger
Johnston reveals. The good news: we can stop it.
By Roger Johnston (as told to Suzanne LaBarre)
Posted November 5, 2012

Vulnerability Assessment Team at Argonne National Lab
A simple non-cyber attack on an electronic voting machine
Roger Johnston is the head of the Vulnerability Assessment Team
at Argonne National Laboratory. Not long ago, he and his colleagues
launched security attacks on electronic voting machines to demonstrate
the startling ease with which one can steal votes. Even more startling:
Versions of those machines will appear in polling places all over
America on Tuesday. The touchscreen Diebold Accuvote-TSX will be used by
more than 26 million voters in 20 states; the push-button Sequoia AVC
Voting Machine will be used by almost 9 million voters in four states, Harper’s magazine reported recently
(subscription required). Here, Johnston reveals how he hacked the
machines–and why anyone, from a high-school kid to an 80-year-old
grandmother, could do the same.–Ed
The Vulnerability Assessment Team at Argonne
National Laboratory looks at a wide variety of security devices– locks,
seals, tags, access control, biometrics, cargo security, nuclear
safeguards–to try to find vulnerabilities and locate potential fixes.
Unfortunately, there’s not much funding available in this country to
study election security. So we did this as a Saturday afternoon type of
project.
It’s called a man-in-the-middle attack. It’s a classic attack on
security devices. You implant a microprocessor or some other electronic
device into the voting machine, and that lets you control the voting and
turn cheating on and off. We’re basically interfering with transmitting
the voter’s intent.
We used a logic analyzer. Digital communication is a series of zeros
and ones. The voltage goes higher, the voltage goes lower. A logic
analyzer collects the oscillating voltages between high and low and then
will display for you the digital data in a variety of formats. But
there all kinds of way to do it. You can use a logic analyzer, you can
use a microprocessor, you can use a computer–basically, anything that
lets you see the information that’s being exchanged and then lets you
know what to do to mimic the information.
I’ve been to high school science fairs where the kids had more
sophisticated microprocessor projects.So we listened to the
communications going on between the voter, who in the case of one
machine is pushing buttons (it’s a push-button voting machine) and in
the other is touching things on a touchscreen. Then we listened to the
communication going on between the smarts of the machine and the voter.
Let’s say I’m trying to make Jones win the election, and you might vote
for Smith. Then my microprocessor is going to tell the smarts of the
machine to vote for Jones if you try to vote for Smith. But if you’re
voting for Jones anyway, I’m not going to tamper with the
communications. Sometimes you block communications, sometimes you tamper
with information, sometimes you just look at it and let it pass on
through. That’s essentially the idea. Figure out the communications
going on, then tamper as needed, including with the information being
sent back to the voter.
We can do this because most voting machines, as far as I can tell,
are not encrypted. It’s just open standard format communication. So it’s
pretty easy to figure out information being exchanged. Anyone who does
digital electronics–a hobbyist or an electronics fan–could figure this
out.
The device we implanted in the touchscreen machine was essentially
$10 retail. If you wanted a deluxe version where you can control it
remotely from a half a mile away, it’d cost $26 retail. It’s not big
bucks. RadioShack would have this stuff. I’ve been to high school
science fairs where the kids had more sophisticated microprocessor
projects than the ones needed to rig these machines.
Because there’s no funding for this type of security-testing, we
relied on people who buy used machines on eBay [in this case the
touchscreen Diebold Accuvote TS Electronic Voting Machine and the
push-button Sequoia AVC Advantage Voting Machine]. Both of the machines
were a little out-of-date, and we didn’t have user manuals and circuit
diagrams. But we figured things out, in the case of the push-button
machine, in under two hours. Within 2 hours we had a viable attack. The
other machine took a little longer because we didn’t fully understand
how touchscreen displays worked. So we had learning time there. But that
was just a couple days. It’s like a magic trick. You’ve got to practice
a lot. If we practiced a lot, or even better, if we got someone really
good with his hands who practiced a lot for two weeks, we’re looking at
15 seconds to 60 seconds go execute these attacks.
I want to move it to the point where grandma can’t hack elections.
We’re really not there.The attacks require physical access. This is easy
for insiders, who program the machines for an election or install them.
And we would argue it’s typically not that hard for outsiders. A lot of
voting machines are sitting around in the church basement, the
elementary school gymnasium or hallway, unattended for a week or two
before the election. Usually they have really cheap cabinet locks anyone
can pick; sometimes they don’t even have locks on them. No one signs
for the machines when they show up. No one’s responsible for watching
them. Seals on them aren’t much different from the anti-tamper packaging
found on food and over-the-counter pharmaceuticals. Think about
tampering with a food or drug product: You think that’s challenging?
It’s really not. And a lot of our election judges are little old ladies
who are retired, and God bless them, they’re what makes the elections
work, but they’re not necessarily a fabulous workforce for detecting
subtle security attacks.
Give people checking the seals a little training as to what to look
for, and now they have a chance to detect a reasonably sophisticated
attack. Do good background checks on insiders, and that insider threat
would be much less of a concern. Overall, there’s a lack of a good
security culture. We can have flawed voting machines, but if we have a
good security culture, we can still have good elections. On the other
hand, we can have fabulous machines, but if the security culture is
inadequate, it doesn’t really matter. We’ve really got to look at a
bigger picture. Our view is: It’s always going to be hard to stop James
Bond. But I want to move it to the point where grandma can’t hack
elections, and we’re really not there.
Watch the Video:
http://www.popsci.com/gadgets/article/2012-11/how-i-hacked-electronic-voting-machine
Proof No 18
http://arstechnica.com/tech-policy/2015/04/meet-the-e-voting-machine-so-easy-to-hack-it-will-take-your-breath-away/

Meet the e-voting machine so easy to hack, it will take your breath away
Virginia decertifies device that used weak passwords and wasn’t updated in 10 years.

Virginia election officials have decertified an electronic voting
system after determining that it was possible for even unskilled people
to surreptitiously hack into it and tamper with vote counts.
The AVS WINVote,
made by Advanced Voting Solutions, passed necessary voting systems
standards and has been used in Virginia and, until recently, in
Pennsylvania and Mississippi. It used the easy-to-crack passwords of
“admin,” “abcde,” and “shoup” to lock down its Windows administrator
account, Wi-Fi network, and voting results database respectively,
according to a scathing security review published Tuesday
by the Virginia Information Technologies Agency. The agency conducted
the audit after one Virginia precinct reported that some of the devices
displayed errors that interfered with vote counting during last
November’s elections.
The weak passwords—which are hard-coded and can’t be changed—were
only one item on a long list of critical defects uncovered by the
review. The Wi-Fi network the machines use is encrypted with wired equivalent privacy,
an algorithm so weak that it takes as little as 10 minutes for
attackers to break a network’s encryption key. The shortcomings of WEP
have been so well-known that it was banished in 2004 by the IEEE,
the world’s largest association of technical professionals. What’s
more, the WINVote runs a version of Windows XP Embedded that hasn’t
received a security patch since 2004, making it vulnerable to scores of
known exploits that completely hijack the underlying machine. Making
matters worse, the machine uses no firewall and exposes several
important Internet ports.
“Because the WINVote devices use insecure security protocols, weak
passwords, and unpatched software, the WINVote devices operate with a
high level of risk,” researchers with the Virginia Information
Technologies Agency wrote in Tuesday’s report. “The security testing by
VITA proved that the vulnerabilities on the WINVote devices can allow a
malicious party to compromise the confidentiality and integrity of
Voting data.”
Putting it to the test
To prove their claim the machine was vulnerable to real-world hacks,
the auditors were able to use the remote desktop protocol to gain remote
access to the voting machines. They also used readily available hacking
and diagnostic software to map, access, and transfer data from default
shared network locations including C$, D$, ADMIN$, and IPC$. After
downloading the database that stores the results of each vote, the
auditors required just 10 seconds to figure out its password was “shoup”
(named after the company name that preceded Advanced Voting Solutions).
The auditors were then able to copy the database, modify its contents
to tamper with recorded votes, and copy it back to the voting machine.
It’s hard to find plain words that convey just how bad the security
of this machine is. It’s even harder to fathom so many critical defects
resided in a line of machines that has played a crucial role in the US’
democratic system for so many years. Jeremy Epstein, a security expert
specializing in e-voting, summarized the threat brilliantly in a post published Wednesday morning to the Freedom to Tinker blog. He wrote:
As one of my colleagues taught me, BLUF—Bottom Line Up
Front. If an election was held using the AVS WinVote, and it wasn’t
hacked, it was only because no one tried. The vulnerabilities were so
severe, and so trivial to exploit, that anyone with even a modicum of
training could have succeeded. They didn’t need to be in the polling
place—within a few hundred feet (e.g., in the parking lot) is easy, and
within a half mile with a rudimentary antenna built using a Pringles
can. Further, there are no logs or other records that would indicate if
such a thing ever happened, so if an election was hacked any time in the
past, we will never know.
He went on to write:
I’ve been in the security field for 30 years, and it
takes a lot to surprise me. But the VITA report really shocked me—as bad
as I thought the problems were likely to be, VITA’s five-page report
showed that they were far worse. And the WinVote system was so fragile
that it hardly took any effort. While the report does not state how much
effort went into the investigation, my estimation based on the
description is that it was less than a person week.
And finally, he wrote:
So how would someone use these vulnerabilities to change an election?
- Take your laptop to a polling place, and sit outside in the parking lot.
- Use a free sniffer to capture the traffic, and use that to figure out the WEP password (which VITA did for us).
- Connect to the voting machine over WiFi.
- If asked for a password, the administrator password is “admin” (VITA provided that).
- Download the Microsoft Access database using Windows Explorer.
- Use a free tool to extract the hardwired key (“shoup”), which VITA also did for us.
- Use Microsoft Access to add, delete, or change any of the votes in the database.
- Upload the modified copy of the Microsoft Access database back to the voting machine.
- Wait for the election results to be published.
It’s good that Virginia will no longer use this machine. Still, given
how long it took for the vulnerabilities to be identified, the report
raises serious questions about the security of electronic voting and the
certification process election officials use to determine if a given
machine can be trusted.
Story updated to change “national” to “necessary” in the second paragraph.
Promoted Comments
Proof No 2
http://www.supremecourtofindia.nic.in/outtoday/wp%28c%29No.161of2004.pdf
Details
Ex
CJI SADHASIVAM, shirked its duty & committed a grave error of
judgment by allowing in phased manner Fraud Tamperable EVMs on the
request of CEC SAMPATH because of Rs.1600 crore cost to replace them
and dealt a fatal blow to the Country’s democracy.
Ex CJI did not order
for ballot paper system to be brought in. No such precautionary measure
was decreed by the apex court. Ex CJI did not order that till the time
this newer set of about 13,00,000 voting machines is manufactured in
full & deployed totally. All the people in 80 democracies in the
world who simply done away with fradulent EVMs should not recognise
Modi & his Government. These Insecure EVMs must be scraped by the CJI to order for Fresh
elections to Lok Sabha and all the State Assembly elections conducted with paper ballots to save
Democracy, Liberty, Fraternity and Equality a Enshrined in the
Constitution.
This act of CJI and CEC helped the Murderer of
democratic institutions (Modi) remotely controlled by 1% chitpawan
brahmin Rowdy Swayam Sevaks gobble the MASTER KEY which goes against the
interest of 99% Sarvajans including SC/STs/OBCs/Minorities/poor upper castes’
liberty, fraternity and equality as enshrined in our Constitution
fathered by Babasaheb Dr BR Ambedkar.
And this
act is itself is proof that the EVMs are vulnerable to fraud for which
they must be punished because of their practice of hatred which is
madness requiring treatment of Insight meditation in mental asylum.
The
present CJI must dismiss the central and all the State Governments
selected by these fraud EVMs and order for fresh elections with paper
ballots which are followed by 80 democracies around the world.
2.
Ms Mayawati who could not win even a single seat in the last Lok sabha
Elections because of the tampering of these fraud EVMs won more than 80 %
votes in the last UP Panchayat elections conducted through paper
ballots. That is another proof of vulnerability of these fraud EVMs.
Therefore,
All the future elections have to be conducted through paper ballots.
Then Ms Mayawati will not only become the CM of UP but also the next PM
of Prabuddha Bharath.
BSP
is not only a political party but also a movement of societal change.
Hence this technological game of 1% Chitpawan RSS plan has to be
defeated by strengthening the 99% intellectuals by exposing the
fradulent EVMs as done by 80 democracies of the world in the larger
interest of Sarvajan Hitaye Sarvajan Sukhaye i.e., for the peace,
happiness and welfare of all societies including SC/STs/ OBCs/
Minorities and the poor brahmins and baniyas for distributing the wealth
of this country among all sections of the society as enshrined in the
Constitution by making the Supreme Court to pass orders to replace all
fradulent EVMs and till such time to scrap all elections conducted by
these fradulent EVMs and then to conduct elections with tamper proof
voting system like paper ballots to save democracy, equality, fraternity and liberty.

Latino Clout Turns on Supreme Court

Loyal leaders who are the Owners of Prabuddha Bharath/Prapanch









+2
The Green leader said: ‘If there is no
one on the ballot paper who you think represents your views, still go
to the polling station and if you want to write a rude word on the
ballot paper’




 Democracy Works
Democracy Works